Before QuillAudits
- Concerns primarily centered around potential vulnerabilities and integrity of the system.
- Potential vulnerabilities in the Signal Service facilitating secure communication between chains.
After QuillAudits
- QuillAudits employed a detailed strategy, utilizing threat modeling, security-focused analysis, comprehensive testing, clear communication, and actionable insights for an effective audit.
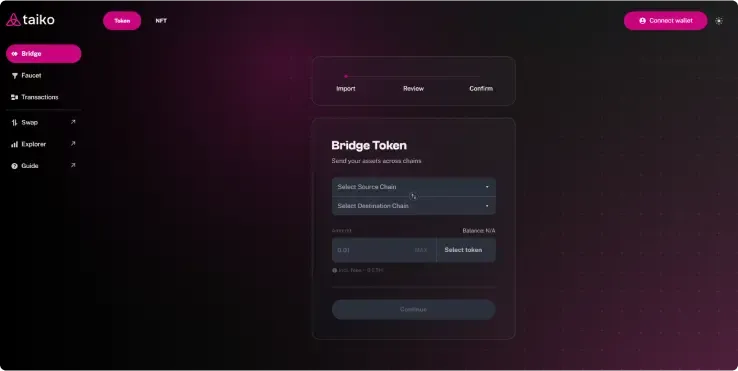
- Addressed Taiko's concerns with rigorous audits of the Bridge, Signal Service, Vaults, and Bridged Tokens.
Get an Audit done today for your Smart Contract
Join 1500+ leaders who secured themselves from losing Billion Dollars


Taiko Protocol features a three-stage process: block proposal, validation, and proving, with open-source MIT licensing for Ethereum L2 security. The driver manages L2 consensus, the proposer initiates transaction proposals, and the prover verifies block validity with ZK-EVM proofs.
Taiko Protocol: Revolutionizing Ethereum Scalability with ZK-EVM
Taiko Protocol emerges as a groundbreaking decentralized Layer 2 blockchain. Leveraging Zero Knowledge Ethereum Virtual Machine (ZK-EVM), it enhances Ethereum's scalability. This is achieved without compromising its core attributes of decentralization, security, and compatibility. As a Type 1 ZK-EVM, it ensures full Ethereum equivalence, providing a frictionless experience for developers.Taiko's methodology encompasses block proposal, validation, and proving stages, underpinning its commitment to security and decentralization. It stands as a fully open-source initiative under the MIT license, poised to redefine Ethereum scalability through its innovative, community-driven approach.
Taiko Protocol: Addressing Bridge, Vault, and Token Security Concerns
The Taiko Protocol encounters several critical issues. One major challenge is guaranteeing the safety of its Bridge contract, which is pivotal for transferring assets across chains. Additionally, there's a need to rectify any vulnerabilities in the Signal Service. This service is crucial for communication between different chains. Protecting Vaults, which store users' funds and tokens, is another significant concern. The protocol must also navigate the complexities related to tokens that symbolize transferred assets. Finally, there's the task of efficiently managing transaction fees within the Bridge contract.
Taiko’s Journey Through our Audit Process
- Information Gathering:
- Collected and reviewed all relevant documentation, including whitepaper, technical specifications, and design documents.
- Obtained a clear understanding of the taiko platform's functionality, Bridge, Vault, and intended user interactions.
- Discussed client concerns and specific areas of focus for the audit.
- Manual Code Review:
- Conducted a line-by-line review of the smart contract code, focusing on:
- Vulnerability identification: Searching for known vulnerabilities like reentrancy, front-running, integer overflows, and access control issues, etc.
- Logic flaws: Identifying inconsistencies or unintended behaviours in the code logic.
- Solidity best practices: Compliance with secure coding standards and adherence to established guidelines
- Conducted a line-by-line review of the smart contract code, focusing on:
- Functional Testing:
- Developed and executed a comprehensive set of test cases covering various user interactions and edge cases.
- Leveraged tools like Hardhat and Ganache to deploy and test the smart contract locally
Highlights of Tests we carried out in Functional testing
Bridge: - Sending native tokens: Verified user capability to send native tokens across chains.
- Retrying messages: Tested user ability to retry failed messages Recalling messages: Confirmed user ability to recall messages before processing.
- Chain validation: Ensured proper transaction reverts if message destination chain or retry chain mismatch.
- Source chain validation: Verified transaction reverts for message recalling on a different source chain.
- Signal verification: Confirmed transaction reverts on signal service verification failure.
- Status updates: Assessed accurate updates of message status during processing, retrying, and recalling.
- Unauthorized access prevention: Confirmed inability to execute transactions on Bridge or Signal Service without authorization
ERC20Vault: - Cross-chain transfers: Verified successful transfers of canonical tokens and bridge tokens across chains (both ways).
- Recalls: Confirmed successful retrieval of recalled canonical tokens.
- Bridge token change: Verified owner’s ability to modify the bridge token associated with the vault.
ERC721Vault and ERC1155Vault: - Functionality parity: All functionality testing performed on ERC20Vault was replicated for both ERC721 and ERC1155 vaults, ensuring consistency across token standards.
- Automated Testing:
- Employed static analysis tools like Slither to identify vulnerabilities through automated code scanning.
- Utilized symbolic execution tools like Mythril to explore various code execution paths and uncover potential attack vectors.
- Integrated unit tests are written by the Taiko team to verify specific contract functions and their behaviour
- Reporting & Remediation:
- Prepared a detailed report outlining all identified vulnerabilities, categorized by severity and potential impact.
- Provided clear recommendations for fixing each vulnerability, including code snippets and best practices.
- Collaborated with the Taiko team to prioritize and address the identified issues.
- Conducted additional verification testing after vulnerability fixes were implemented.
QuillAudits' Strategic Approach to Taiko’s Security Audits
Our methodology for Taiko Smart Contracts combines threat modeling, a security-first mindset, and comprehensive testing, including both white-box and black-box methods. We emphasize transparency and clear communication with the Taiko team, providing actionable insights and detailed recommendations for swift vulnerability resolution, ensuring a robust security posture.
Comprehensive Audit Discoveries and Remediation Strategies
Our thorough and extensive audit uncovered 4 critical vulnerabilities, 6 low-severity issues, and 5 informational findings.
Some of the high-severity vulnerabilities included:
- Unverified arbitrary data call : This vulnerability allowed attackers to bypass essential validations and inject malicious data directly into the system.
- Unchecked transfer : This could have led to users losing funds intended for transaction fees.
- Permanent fund loss : Users risked permanently losing their bridged tokens if message decoding failed.
- Bridged token recall issue : The system lacked the functionality to recall bridged tokens.
Following the detailed review, we met with Taiko developers to explain each identified issue, its potential impact and proposed effective remedies.
The security audit of Taiko smart contracts was instrumental in identifying and mitigating critical vulnerabilities. This effort significantly enhanced the protection of user funds and the overall stability of the platform.This case emphasizes the importance of proactive security in blockchain projects, especially those managing financial assets. Taiko's prompt action in resolving these issues exemplifies their commitment to platform security and user trust.