Drift Protocol $285M Multisig Exploit (Explained)
Breaking down Drift Protocol’s $285M hack, multisig risks, exploit mechanics and actionable DeFi security lessons.

On April 1, 2026, Drift Protocol, one of Solana's largest perpetual DEXs with over $550M in TVL, was hit by a $285M exploit. This wasn't a smart contract vulnerability. The attacker social-engineered two out of five multisig signers into pre-signing malicious transactions using Solana's durable nonce feature, then used those signatures to hijack admin control and drain the vaults in under 12 minutes. It stands as the largest DeFi hack of 2026 and the second-largest in Solana's history behind the Wormhole bridge exploit.
Hack Analysis
This wasn’t a smart contract bug, it was a social engineering attack. Between March 23 - 30, multiple durable nonce accounts were created across both multisig members and attacker-controlled wallets, suggesting that at least 2/5 signers had been compromised, even after the planned Security Council migration on March 27.
Despite the migration, the attacker maintained access within the updated multisig and continued preparing nonce-based transactions for delayed execution.
Shortly after, they used these pre-signed transactions to take over admin control and execute the exploit within minutes.
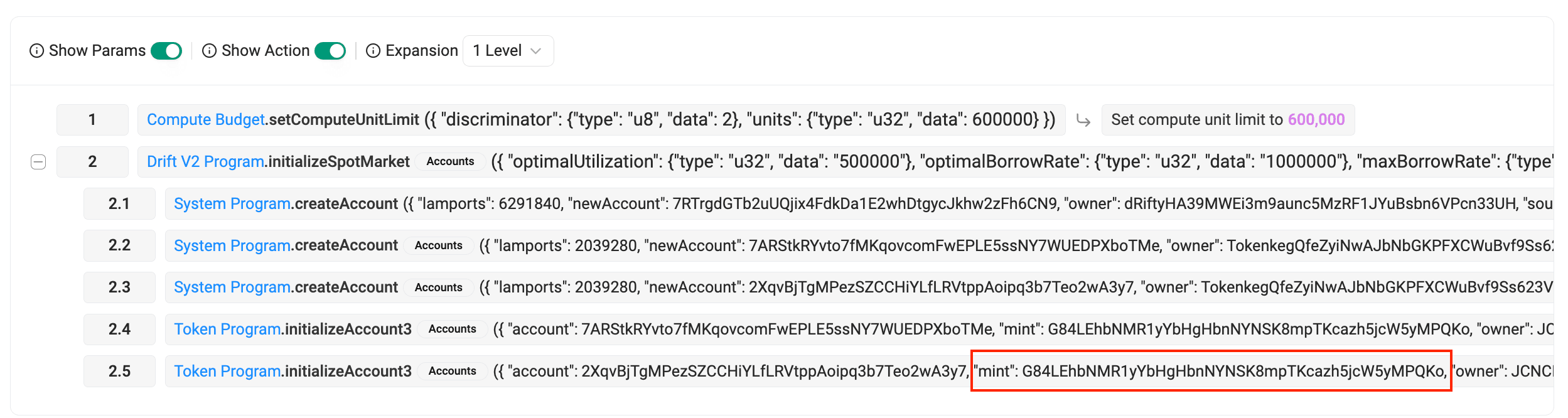
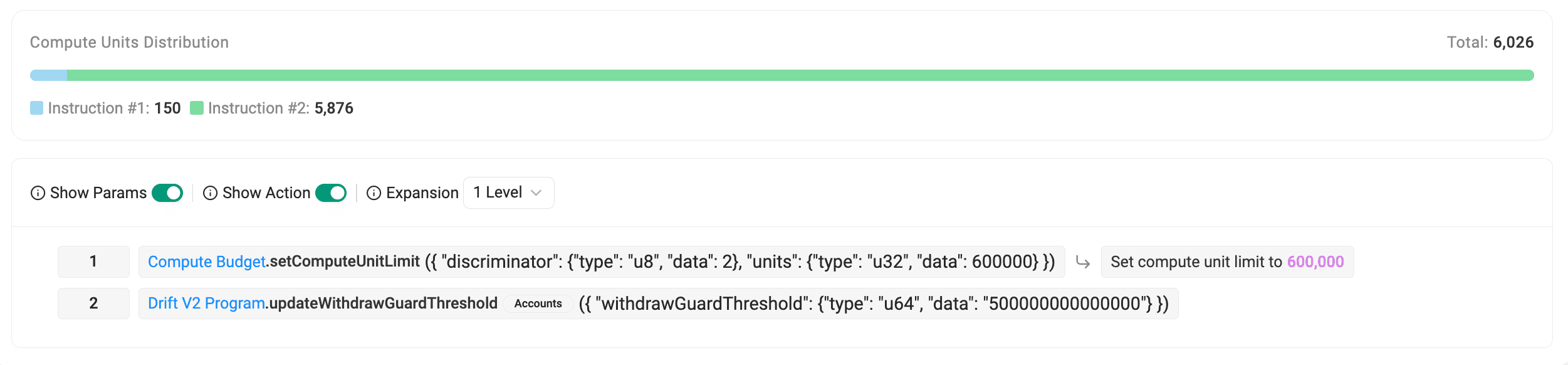
With admin access, the attacker created multiple spot markets using a fake token (CVT), set up manipulated oracles under their control, and modified withdrawal limits.
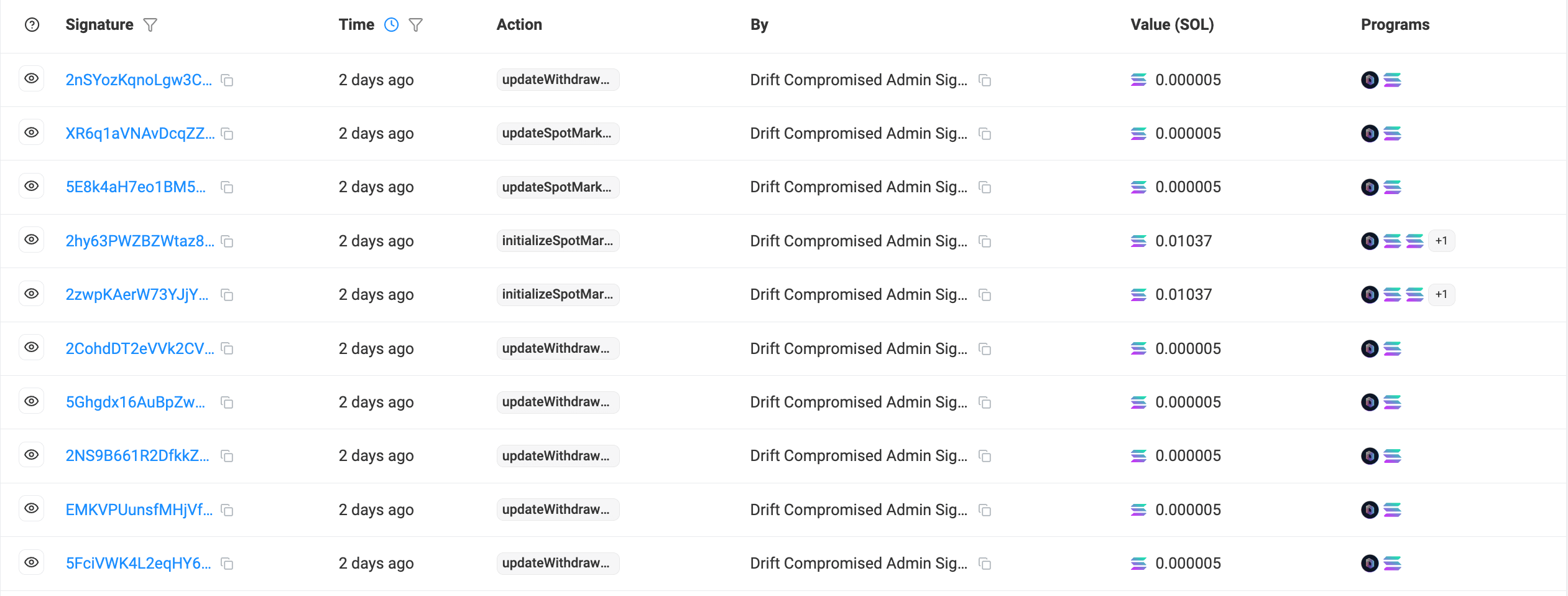

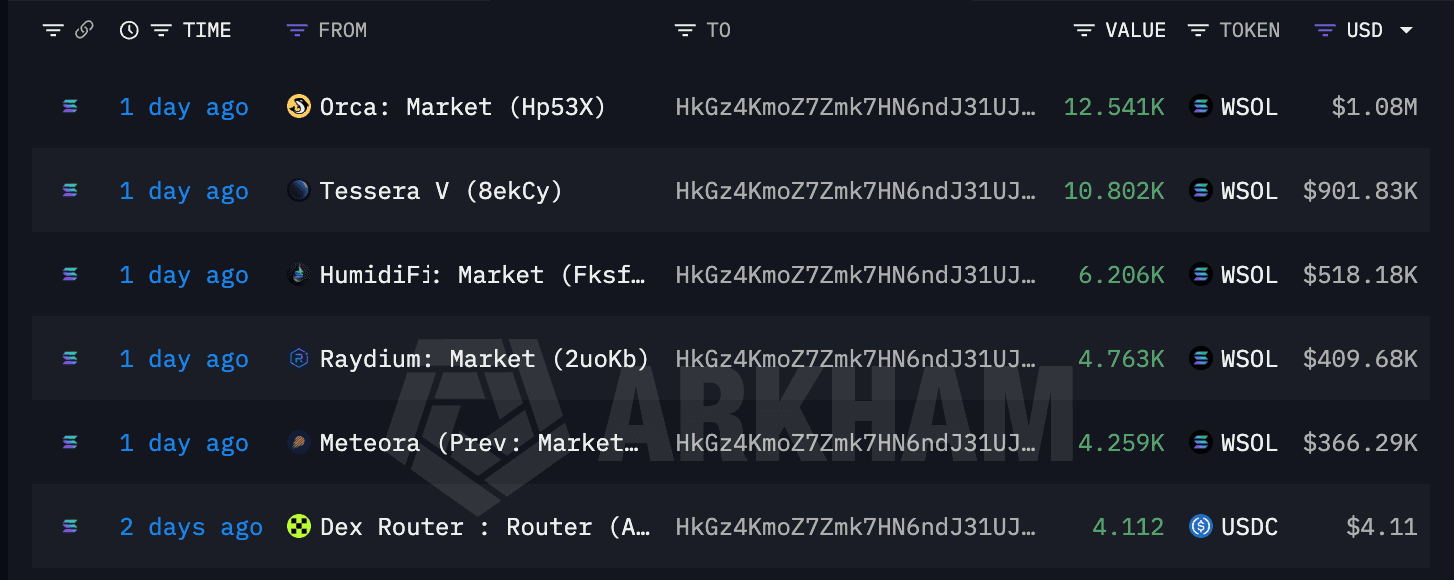
Using a second account (HkGz4KmoZ7Zmk7HN6ndJ31UJ1qZ2qgwQxgVqQwovpZES), the attacker began draining the vault by posting the fake CVT token as collateral and borrowing real assets against it. Since both the oracle and the CVT supply were under their control, the borrow appeared legitimate within the system.
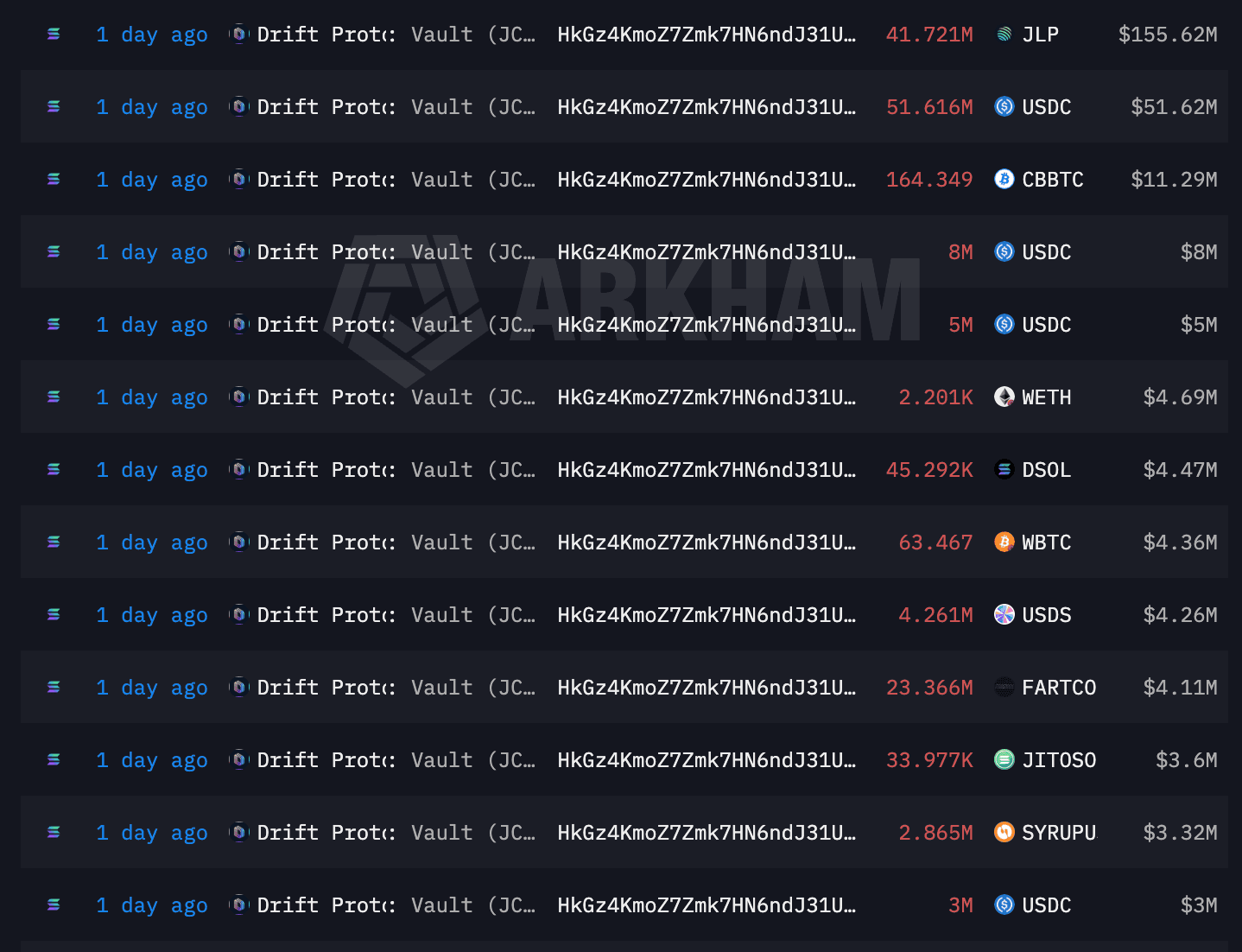
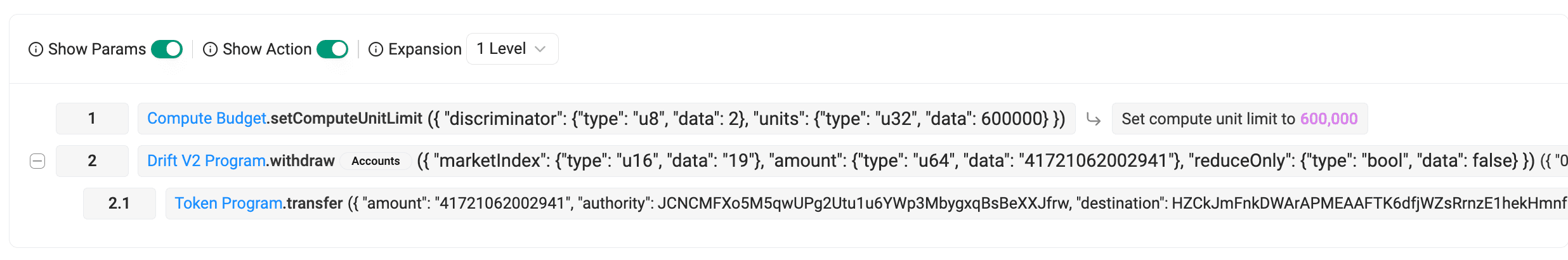
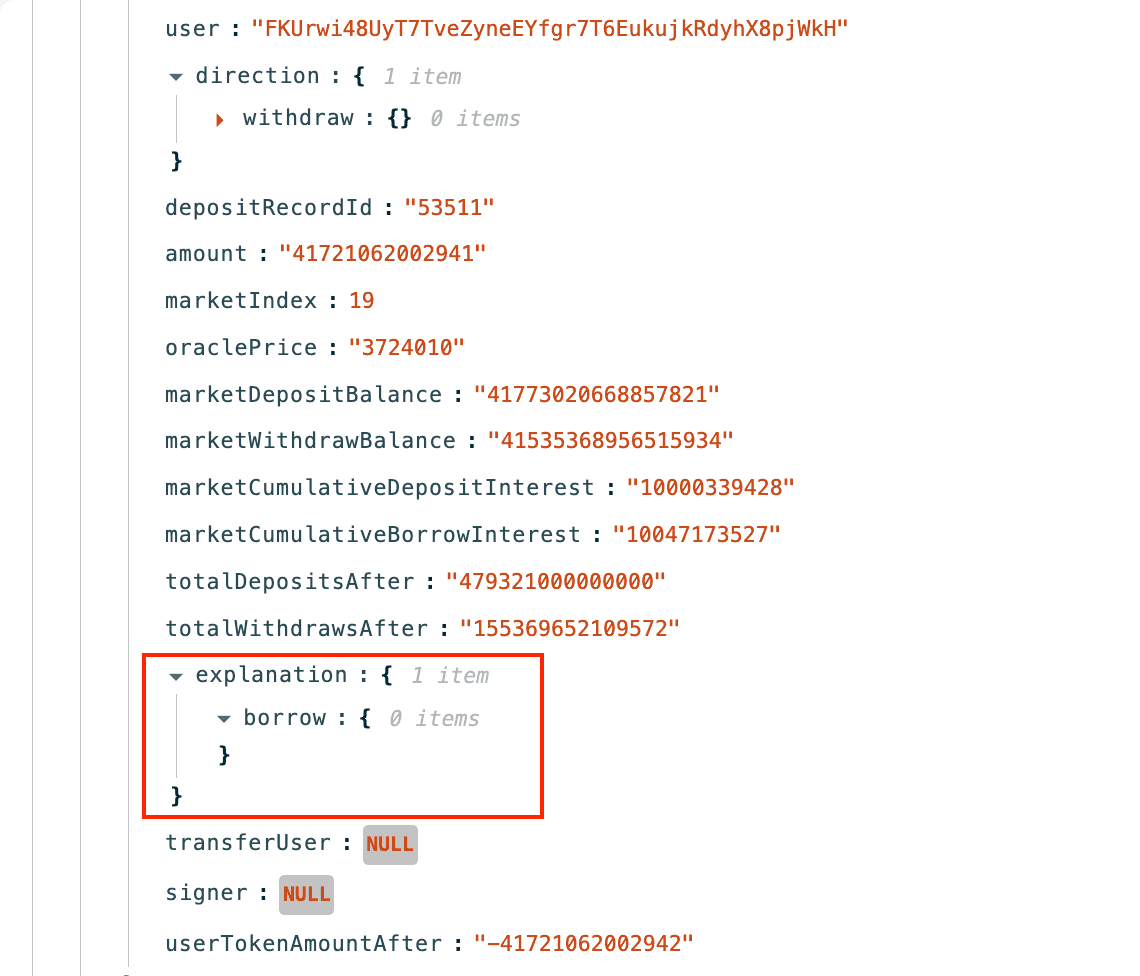
By repeatedly executing this borrow loop through 33 transactions, the attacker drained the vault, extracting over $285M across multiple tokens. Below is the complete breakdown of token amounts and their corresponding dollar value.

| Token | Amount | USD Value |
|---|---|---|
| JLP | 42.72M | $159.35M |
| USDC | 71.42M | $71.42M |
| cbBTC | 164.35 | $11.29M |
| USDT | 5.65M | $5.65M |
| USDS | 5.25M | $5.25M |
| WETH | 2,200.59 | $4.69M |
| dSOL | 45,292.21 | $4.47M |
| WBTC | 63.47 | $4.36M |
| Fartcoin | 23.37M | $4.11M |
| JitoSOL | 33,976.51 | $3.60M |
| syrupUSDC | 2.87M | $3.32M |
| INF | 21,241.62 | $2.50M |
| mSOL | 17,418.92 | $1.99M |
| bsol | 9,474.33 | $1.02M |
| EURC | 583,980.69 | $677.42K |
| zBTC | 8.61 | $586.79K |
| USDY | 477,375.42 | $539.43K |
| JUP | 2.62M | $431.44K |
| WSOL | 0.03 | $2.74 |
| Total | $285.26M |
Root Cause
The Drift exploit was not caused by a bug in the protocol's smart contracts. It was an operational security failure rooted in a poorly configured multisig and social engineering.
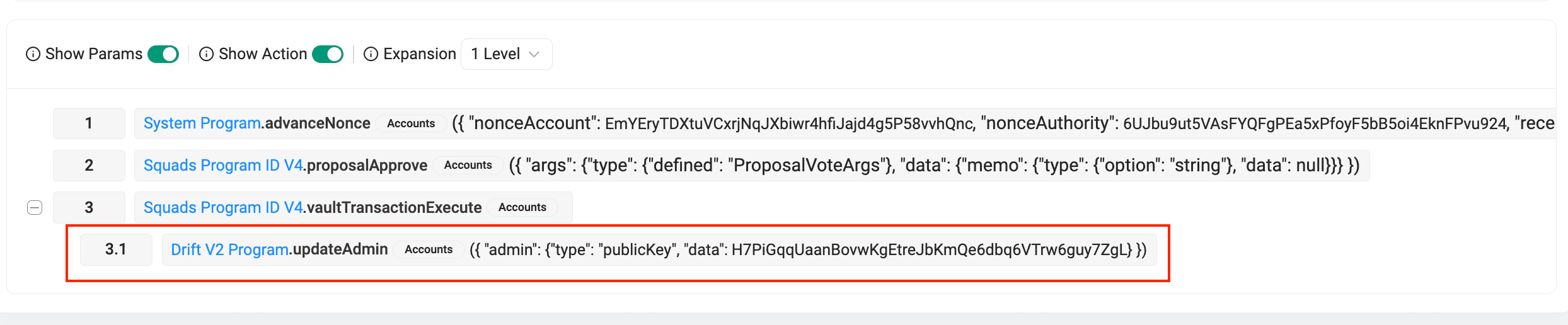
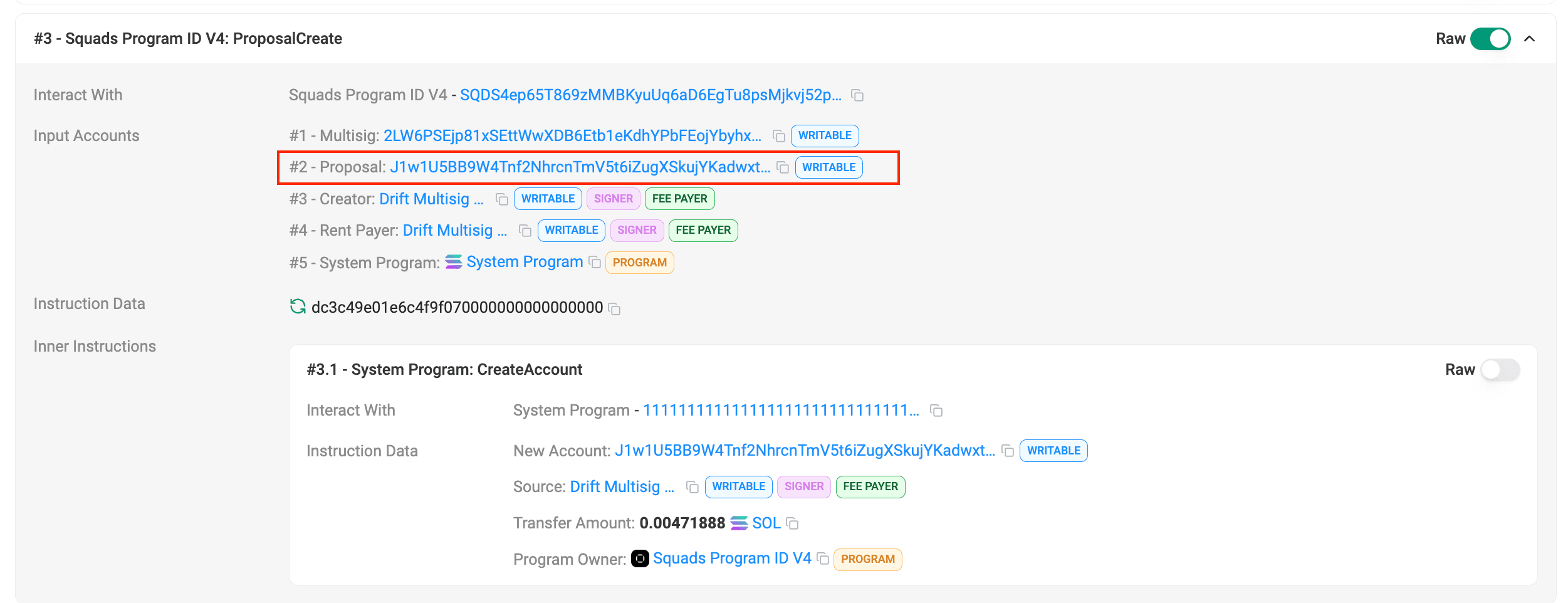
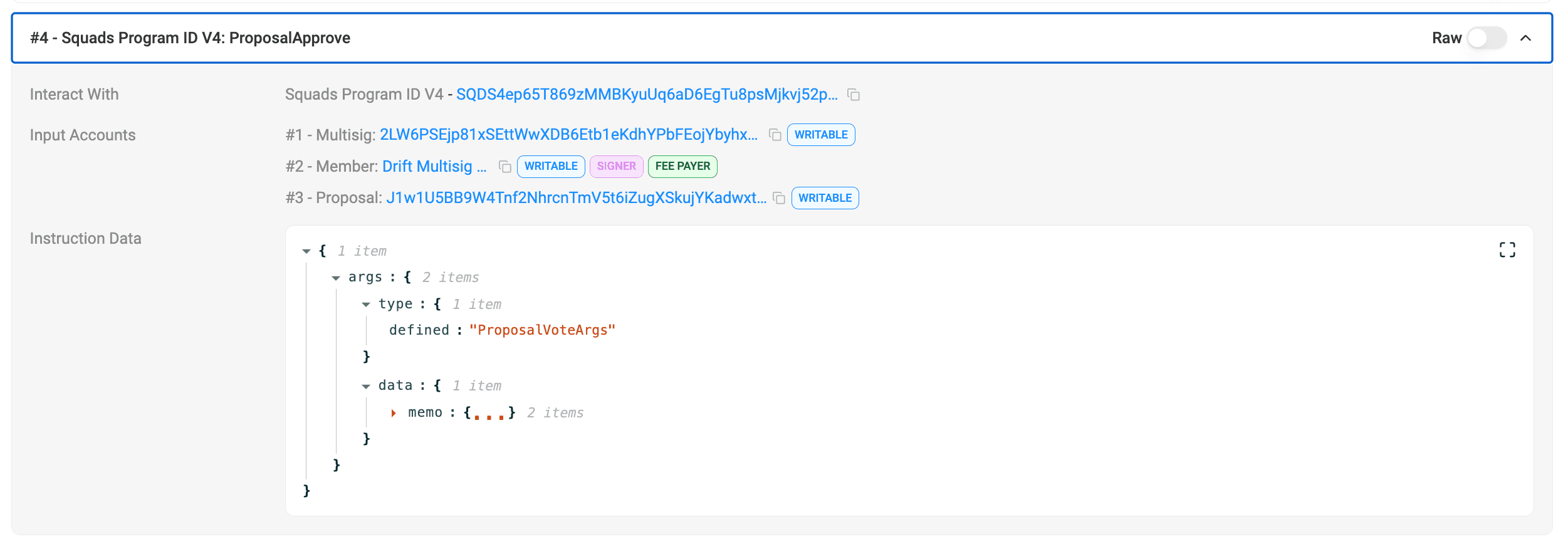
Drift's Security Council ran on a Squads V4 multisig with a 2/5 signing threshold. On-chain records show exactly how this played out, at block 410344005 (16:05:18 UTC), the first transaction created the malicious proposal and recorded the first approval. Just one second later at block 410344009 (16:05:19 UTC), the second transaction carried the approval and immediately executed the admin transfer in the same atomic transaction, with no timelock to delay execution after the threshold was met.
The attacker exploited Solana's durable nonce feature to collect these signatures days before the actual attack. Durable nonces bypass the standard ~60 second blockhash expiry on Solana, allowing signed transactions to remain valid indefinitely. Between March 23 and March 30, the attacker created nonce accounts tied to at least two multisig members and likely tricked them into signing what appeared to be routine transactions. These were actually payloads for an admin transfer.
On March 27, Drift migrated its Security Council multisig, swapping most signers and keeping only one from the old set. Instead of closing the attack window, this created a second one. Within three days, the attacker had re-established nonce based access to two signers on the new multisig.
When the attack triggered on April 1, everything was already in place. Two pre-signed transactions, submitted one second apart, transferred full admin control to the attacker. From there, they created fake spot markets using a worthless token (CVT), disabled circuit breakers, removed withdrawal limits, and drained over $285M through 33 borrow-loop transactions, all within minutes.

How QuillAudits On-Chain Monitoring Could Have Prevented This
QuillAudits' on-chain monitoring system tracks real-time administrative changes, multisig activity, and abnormal fund movements, exactly the kind of signals this attack produced.
Durable nonce account creation detection. The attacker created multiple durable nonce accounts between March 23 - 30 linked to multisig signers. On-chain monitoring would have flagged unusual nonce account activity tied to privileged addresses, raising an alert days before the exploit.
Multisig configuration change alerts. When Drift migrated its Security Council on March 27 with a 2/5 threshold and zero timelock, monitoring would have flagged this as a high-risk governance change for a protocol holding $550M+ in TVL.
Admin transfer detection. The moment the admin authority was transferred to an unknown address, at 16:05 UTC, real-time alerts would have triggered immediate incident response, potentially before the attacker could disable circuit breakers and begin draining.
Abnormal withdrawal pattern detection. The attacker executed 33 rapid borrow-loop transactions to drain the vault. Monitoring systems tracking withdrawal velocity and volume against historical baselines would have flagged this within the first few transactions, enabling faster intervention by bridge operators and stablecoin issuers like Circle to freeze assets in transit.
Fake market and oracle manipulation alerts. The creation of new spot markets (CVT) with an unrecognized token and an attacker-controlled oracle would have been detected as anomalous, especially when collateral weights were immediately set to maximum values in the same transaction.
With QuillAudits monitoring in place, the attack window between admin takeover and fund drainage, roughly 10 minutes, could have been significantly compressed, and downstream laundering through Jupiter, CCTP, and Wormhole could have been disrupted much earlier.
Funds Flow After Attack
The attacker drained over $285M across multiple tokens, then swapped most of it into USDC, WSOL, WBTC, and WETH using Jupiter Protocol.
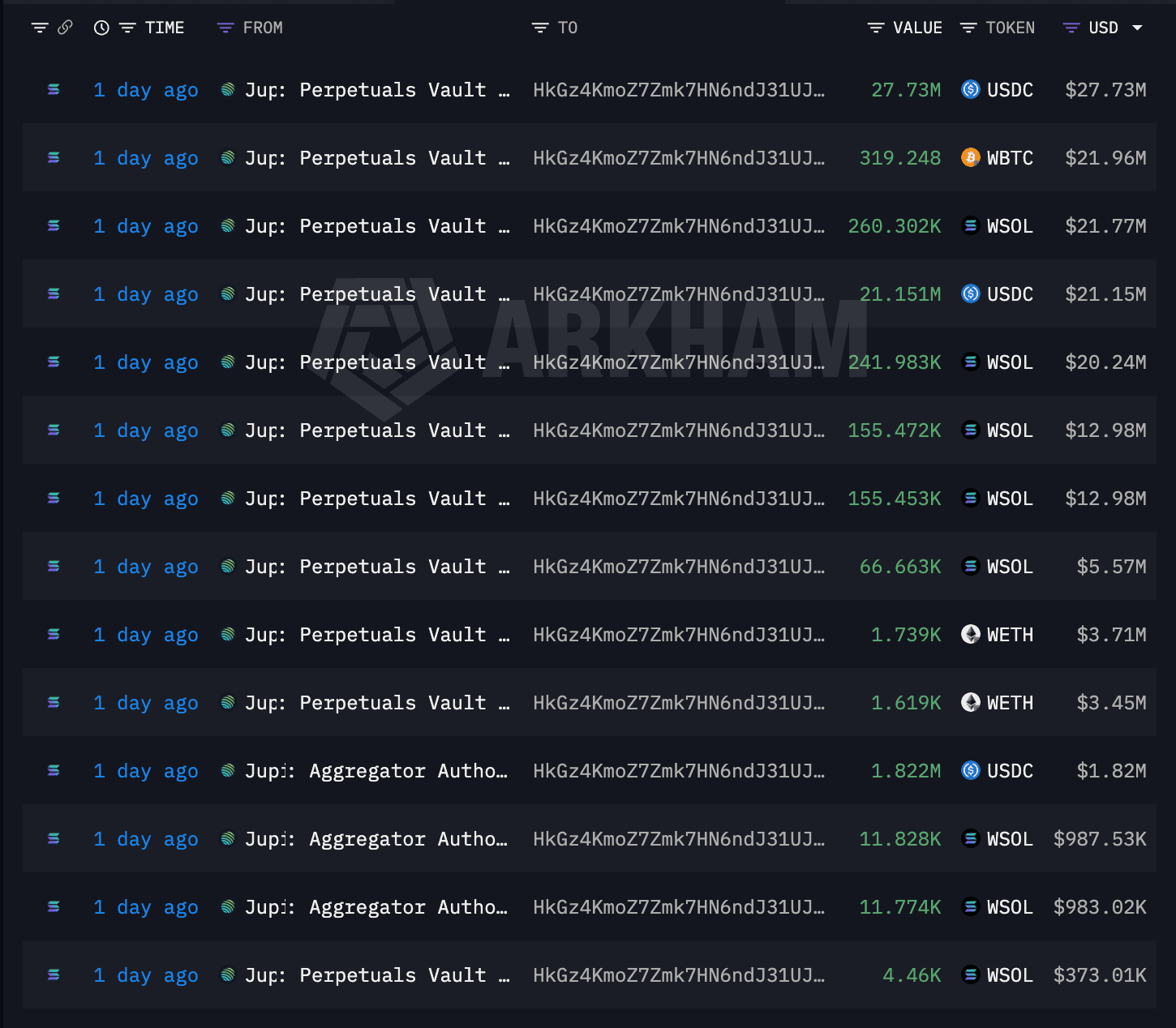
The attacker followed a classic playbook—splitting funds across multiple wallets and then moving them further to create a complex web of transactions.

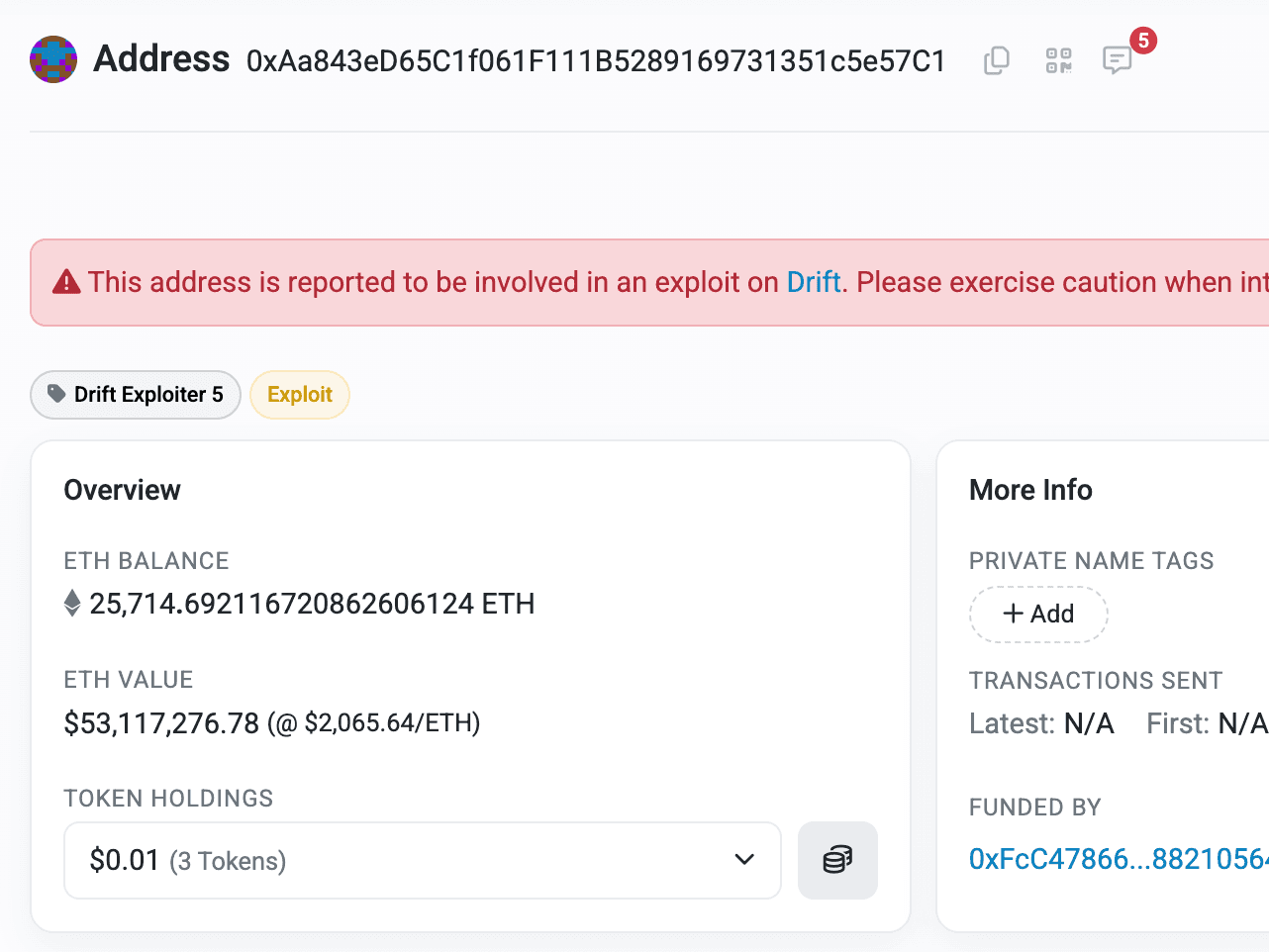
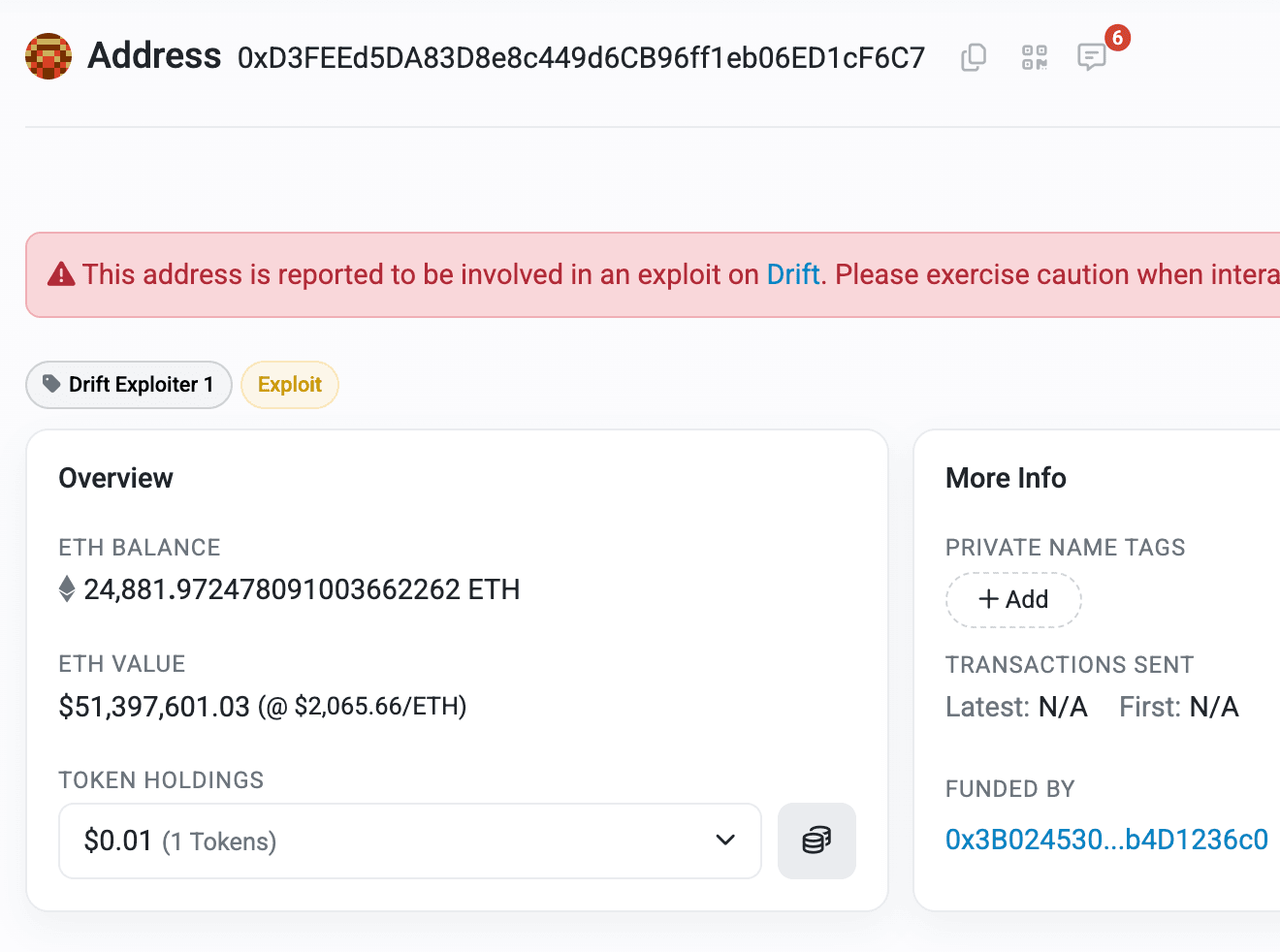
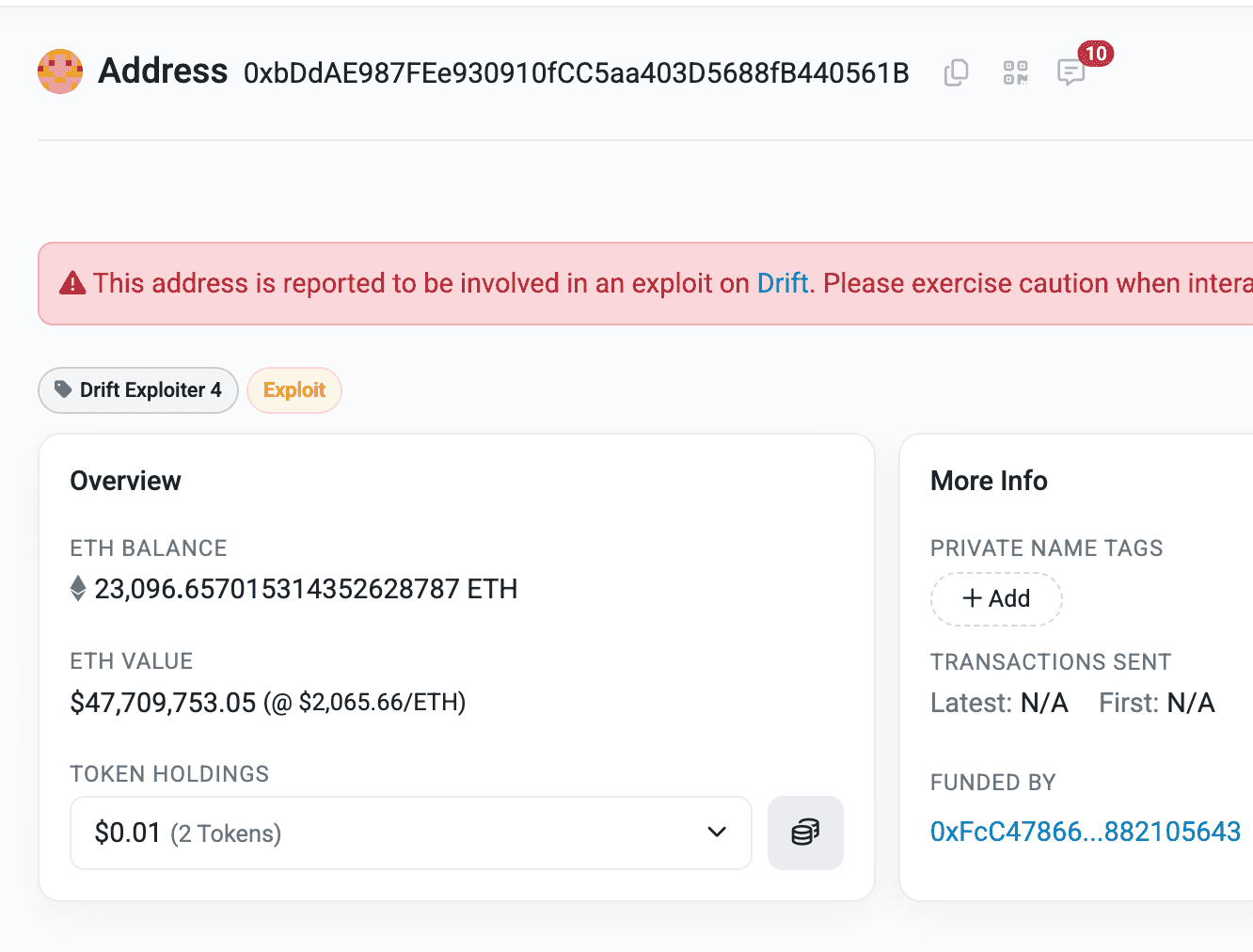
After all the swaps and layered transfers, the attacker bridged the funds to Ethereum, consolidating everything into ETH. The assets are now sitting across four attacker-controlled EOAs.

Post Attack Mitigation
The team had confirmed an active attack, paused deposits and withdrawals, and is working closely with security partners to contain the incident as quickly as possible.
After the pause, the team shared the root cause along with a Twitter-based postmortem.
The team is also reaching out to the attacker via blockscan chat in an attempt to negotiate.
Relevant Address and Transactions
Attacker EOAs Ethereum
- 0xAa843eD65C1f061F111B5289169731351c5e57C1
- 0xD3FEEd5DA83D8e8c449d6CB96ff1eb06ED1cF6C7
- 0xbDdAE987FEe930910fCC5aa403D5688fB440561B
- 0x0FE3b6908318B1F630daa5B31B49a15fC5F6B674
Attacker Account Solana
Drift Vault
JCNCMFXo5M5qwUPg2Utu1u6YWp3MbygxqBsBeXXJfrw
Drift Vault State
5zpq7DvB6UdFFvpmBPspGPNfUGoBRRCE2HHg5u3gxcsN
Drift V2 Program
dRiftyHA39MWEi3m9aunc5MzRF1JYuBsbn6VPcn33UH
Admin Update Transactions
- 2HvMSgDEfKhNryYZKhjowrBY55rUx5MWtcWkG9hqxZCFBaTiahPwfynP1dxBSRk9s5UTVc8LFeS4Btvkm9pc2C4H
- 4BKBmAJn6TdsENij7CsVbyMVLJU1tX27nfrMM1zgKv1bs2KJy6Am2NqdA3nJm4g9C6eC64UAf5sNs974ygB9RsN1
Drift Vault Arkham Profile
JCNCMFXo5M5qwUPg2Utu1u6YWp3MbygxqBsBeXXJfrw
Conclusion
The Drift exploit is a clear example of how operational security failures can bypass even audited smart contracts. A weak 2/5 multisig threshold, zero timelock, and the abuse of durable nonces gave the attacker everything they needed. No code was broken, governance was. For protocols managing hundreds of millions, real-time on-chain monitoring, stricter multisig configurations, and signer verification processes are no longer optional, they are the last line of defense.
Contents